COMPANIES COVERED
NXP SemiconductorsDownload FREE Report Sample
Download Free sampleThe Embedded Security Devices market encompasses a range of hardware-based security solutions that protect digital assets, sensitive information, and communications from cyber threats and unauthorized access. These devices integrate cryptographic functions, secure key storage, and authentication mechanisms to enhance data protection. Common categories include Secure Elements (eSE), Embedded SIMs, Trusted Platform Modules (TPM), Hardware Security Modules (HSM), and Hardware Tokens. These technologies are widely used in consumer electronics, automotive, healthcare, industrial IoT, and smart grid applications.
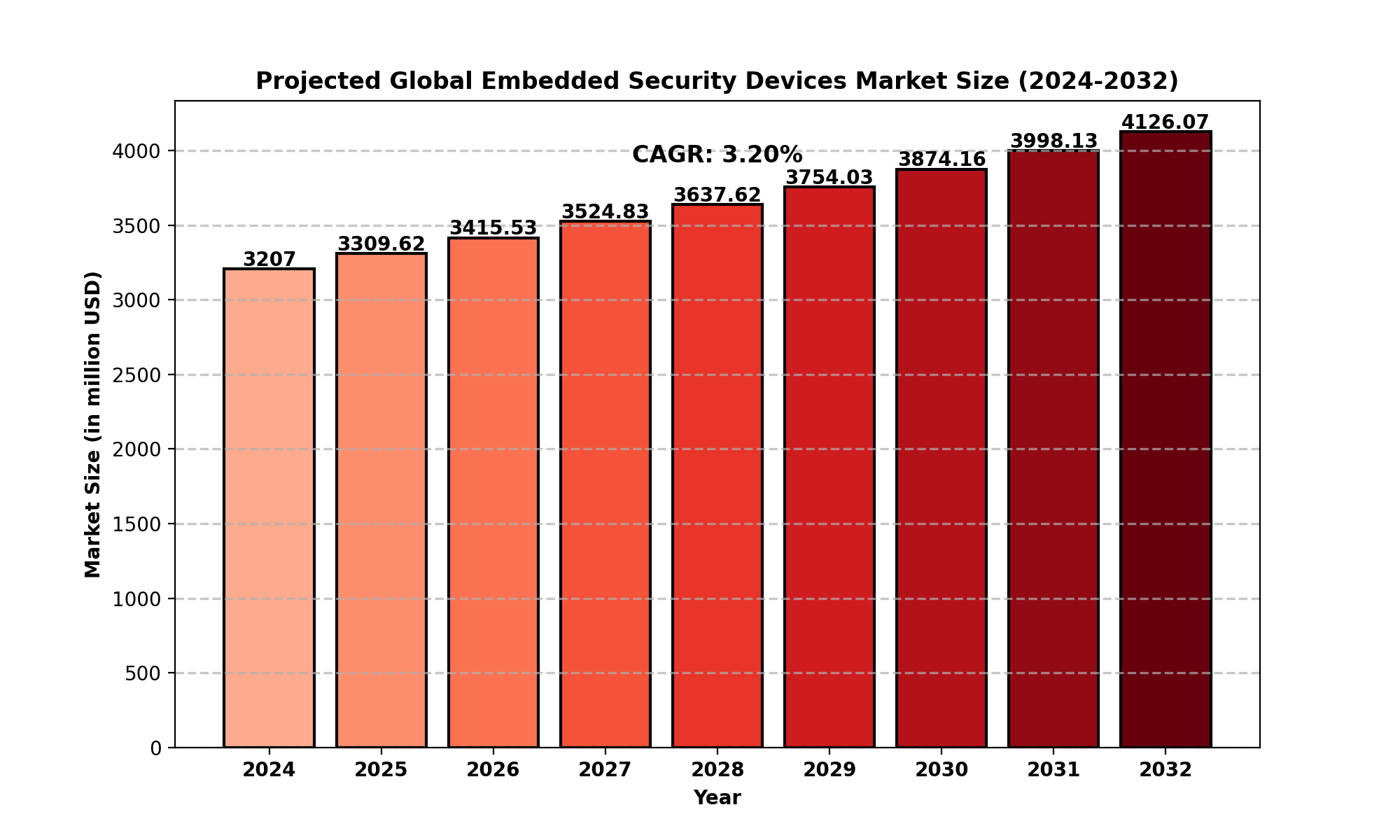
Market Size
As of 2024, the global Embedded Security Devices market is valued at approximately USD 3,207 million, with projections estimating a rise to USD 4,126.07 million by 2032, reflecting a Compound Annual Growth Rate (CAGR) of 3.20%.
North America: USD 882.12 million in 2024, with a CAGR of 2.74%
Europe, Asia-Pacific, South America, and MEA also showcase promising growth potential.
Market Dynamics (Drivers, Restraints, Opportunities, and Challenges)
To know more about market statistics, Download a FREE Sample copy
Drivers
Rising Cybersecurity Threats – The increasing number of cyberattacks on financial transactions, healthcare data, and intellectual property fuels demand for embedded security solutions.
Adoption of IoT and Smart Devices – The proliferation of smart homes, wearables, and connected vehicles boosts the need for integrated security solutions.
Regulatory Compliance and Data Protection Laws – Governments worldwide enforce stringent cybersecurity and data protection regulations, driving adoption.
Advancements in Automotive Security – The shift towards autonomous and connected vehicles necessitates robust security mechanisms.
Restraints
High Implementation Costs – Initial deployment and integration expenses deter small and medium enterprises (SMEs).
Complexity in Deployment – Managing encryption, authentication, and secure key storage across diverse applications poses challenges.
Opportunities
Expansion of 5G and Edge Computing – Accelerates demand for embedded security to protect data at the edge.
Integration with AI and Machine Learning – Enhancing real-time threat detection and mitigation strategies.
Challenges
Evolving Cyber Threats – Sophisticated hacking techniques demand continuous updates and improvements.
Interoperability Issues – Ensuring compatibility across different hardware and software platforms remains a challenge.
Regional Analysis
North America – Market driven by stringent regulatory policies, high adoption of IoT, and increased cyber threats.
Europe – Strong presence of cybersecurity initiatives, particularly in financial and healthcare sectors.
Asia-Pacific – Fastest-growing region due to increasing smartphone penetration and industrial automation.
South America & MEA – Emerging markets witnessing gradual adoption of embedded security technologies.
Competitor Analysis
The market features several key players competing based on technology innovation, product portfolio, and market reach:
NXP Semiconductors – Leading provider of embedded security solutions for IoT, automotive, and industrial applications.
Infineon Technologies – Specializes in secure microcontrollers and Trusted Platform Modules.
STMicroelectronics – Offers a wide range of secure element solutions.
Gemalto (Thales Group) – Focuses on SIM-based and banking security solutions.
Samsung, Intel, Microchip, and Renesas Electronics are also key players shaping the industry.
Market Segmentation (by Application)
Smartphones, Tablets, and Wearables – Secure mobile transactions, biometric authentication, and mobile payments.
Automotive – Keyless entry systems, digital car keys, and vehicle-to-vehicle communication security.
PCs & Servers – Hardware-based authentication and encryption.
Others – Industrial IoT, healthcare devices, and government ID security.
Market Segmentation (by Type)
Embedded Secure Element (eSE) & Embedded SIM – Used in mobile and IoT applications for authentication.
Trusted Platform Module (TPM) – Provides hardware-based security for PCs, servers, and embedded systems.
Key Companies
NXP Semiconductors
Infineon Technologies
STMicroelectronics
Gemalto (Thales Group)
IDEMIA
Maxim Integrated
Renesas Electronics Corporation
Microchip Technology Inc.
Samsung Electronics
Intel Corporation
Nuvoton Technology Corporation
Geographic Segmentation
North America (USA, Canada, Mexico)
Europe (Germany, UK, France, Russia, Italy, Rest of Europe)
Asia-Pacific (China, Japan, South Korea, India, Southeast Asia, Rest of Asia-Pacific)
South America (Brazil, Argentina, Colombia, Rest of South America)
Middle East & Africa (Saudi Arabia, UAE, Egypt, Nigeria, South Africa, Rest of MEA)
FAQ Section
What is the current market size of the Embedded Security Devices Market?
Which are the key companies operating in the Embedded Security Devices Market?
What are the key growth drivers in the Embedded Security Devices Market?
Which regions dominate the Embedded Security Devices Market?
What are the emerging trends in the Embedded Security Devices Market?
Key Benefits of This Market Research:
Industry drivers, restraints, and opportunities covered in the study
Neutral perspective on the market performance
Recent industry trends and developments
Competitive landscape & strategies of key players
Potential & niche segments and regions exhibiting promising growth covered
Historical, current, and projected market size, in terms of value
In-depth analysis of the Embedded Security Devices Market
Overview of the regional outlook of the Embedded Security Devices Market:
Key Reasons to Buy this Report:
Access to date statistics compiled by our researchers. These provide you with historical and forecast data, which is analyzed to tell you why your market is set to change
This enables you to anticipate market changes to remain ahead of your competitors
You will be able to copy data from the Excel spreadsheet straight into your marketing plans, business presentations, or other strategic documents
The concise analysis, clear graph, and table format will enable you to pinpoint the information you require quickly
Provision of market value data for each segment and sub-segment
Indicates the region and segment that is expected to witness the fastest growth as well as to dominate the market
Analysis by geography highlighting the consumption of the product/service in the region as well as indicating the factors that are affecting the market within each region
Competitive landscape which incorporates the market ranking of the major players, along with new service/product launches, partnerships, business expansions, and acquisitions in the past five years of companies profiled
Extensive company profiles comprising of company overview, company insights, product benchmarking, and SWOT analysis for the major market players
The current as well as the future market outlook of the industry concerning recent developments which involve growth opportunities and drivers as well as challenges and restraints of both emerging as well as developed regions
Includes in-depth analysis of the market from various perspectives through Porters five forces analysis
Provides insight into the market through Value Chain
Market dynamics scenario, along with growth opportunities of the market in the years to come
6-month post-sales analyst support
Customization of the Report
In case of any queries or customization requirements, please connect with our sales team, who will ensure that your requirements are met.
Chapter Outline
Chapter 1 mainly introduces the statistical scope of the report, market division standards, and market research methods.
Chapter 2 is an executive summary of different market segments (by region, product type, application, etc), including the market size of each market segment, future development potential, and so on. It offers a high-level view of the current state of the Embedded Security Devices Market and its likely evolution in the short to mid-term, and long term.
Chapter 3 makes a detailed analysis of the market's competitive landscape of the market and provides the market share, capacity, output, price, latest development plan, merger, and acquisition information of the main manufacturers in the market.
Chapter 4 is the analysis of the whole market industrial chain, including the upstream and downstream of the industry, as well as Porter's five forces analysis.
Chapter 5 introduces the latest developments of the market, the driving factors and restrictive factors of the market, the challenges and risks faced by manufacturers in the industry, and the analysis of relevant policies in the industry.
Chapter 6 provides the analysis of various market segments according to product types, covering the market size and development potential of each market segment, to help readers find the blue ocean market in different market segments.
Chapter 7 provides the analysis of various market segments according to application, covering the market size and development potential of each market segment, to help readers find the blue ocean market in different downstream markets.
Chapter 8 provides a quantitative analysis of the market size and development potential of each region from the consumer side and its main countries and introduces the market development, future development prospects, market space, and capacity of each country in the world.
Chapter 9 shares the main producing countries of Embedded Security Devices, their output value, profit level, regional supply, production capacity layout, etc. from the supply side.
Chapter 10 introduces the basic situation of the main companies in the market in detail, including product sales revenue, sales volume, price, gross profit margin, market share, product introduction, recent development, etc.
Chapter 11 provides a quantitative analysis of the market size and development potential of each region during the forecast period.
Chapter 12 provides a quantitative analysis of the market size and development potential of each market segment during the forecast period.
Chapter 13 is the main points and conclusions of the report.

Speak to our Custom Research Team and get the Custom Research in a budget
Custom ResearchFrequently Asked Questions ?
A license granted to one user. Rules or conditions might be applied for e.g. the use of electric files (PDFs) or printings, depending on product.
A license granted to multiple users.
A license granted to a single business site/establishment.
A license granted to all employees within organisation access to the product.
Upto Working 24 to 48 hrs
Upto 72 hrs max - Weekends and Public Holidays
Online Payments with PayPal and CCavenue
Wire Transfer/Bank Transfer
Hard Copy




 Industry Market Size
Industry Market Size SWOT Analysis
SWOT Analysis Industry Major Players
Industry Major Players Revenue Forecasts
Revenue Forecasts Historical and Forecast Growth
Historical and Forecast Growth Profitability Analysis
Profitability Analysis